Information about C2/Generic detections
Current Oncology, Free Full-Text

Instant Detection of Synthetic Cannabinoids on Physical Matrices, Implemented on a Low-Cost, Ultraportable Device

Leptomeningeal Collaterals and Infarct Progression in Patients With Acute Large‐Vessel Occlusion and Low NIHSS

Detection 101: Top 5 Foundational Detection Data Sources
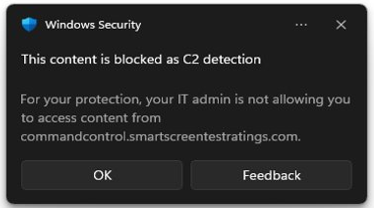
Detection and response to command and control attacks.

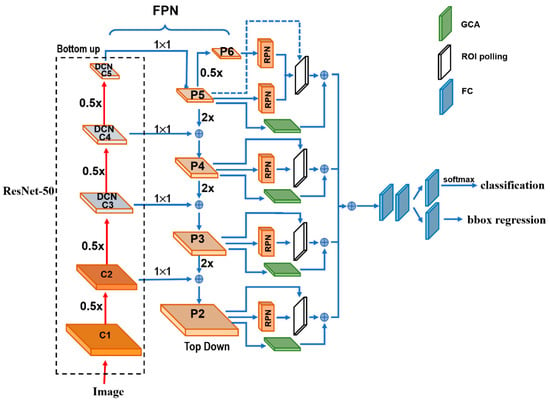
Using AI to Detect Malicious C2 Traffic: Clues About Sophisticated Malware
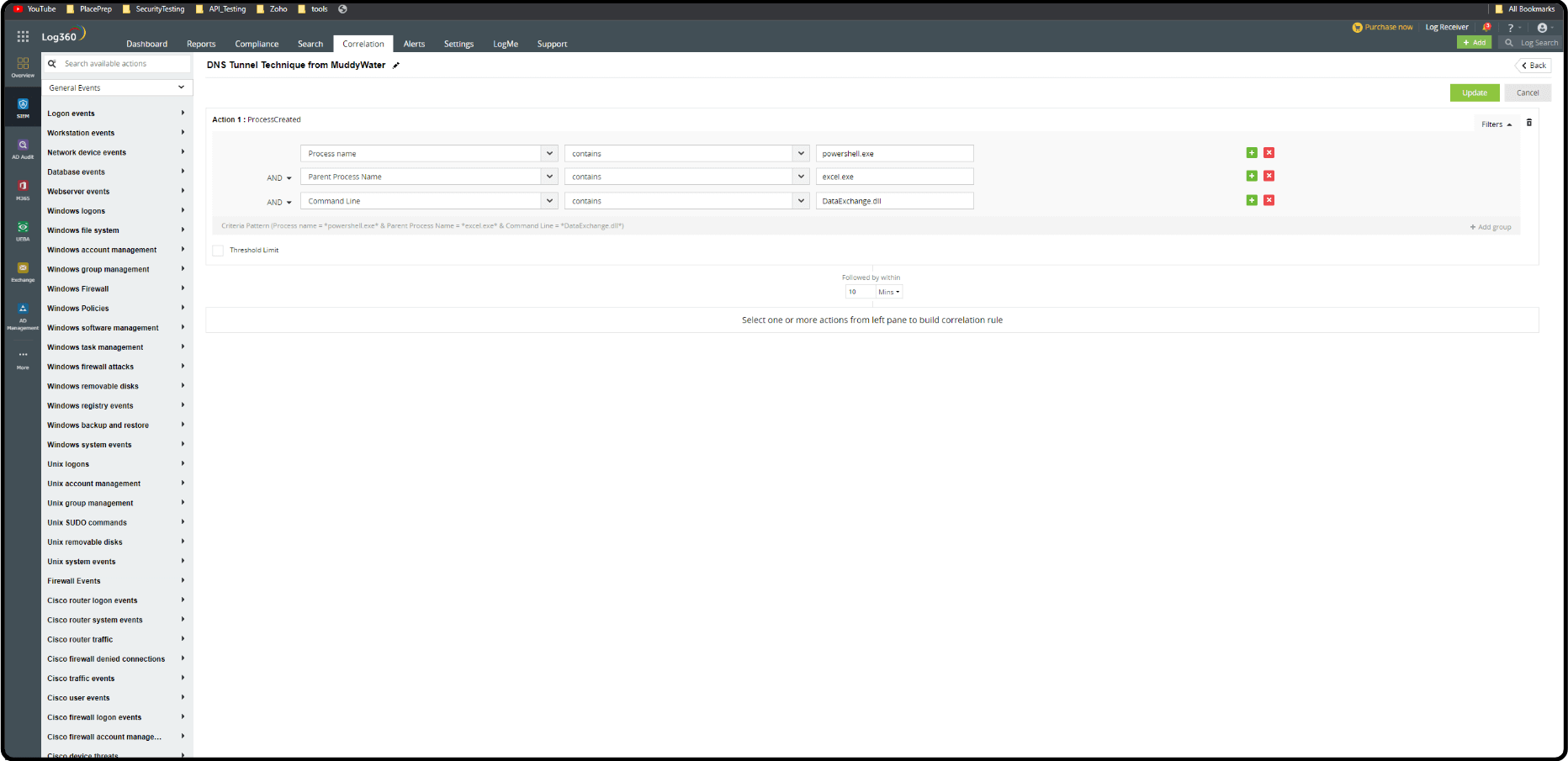
Explore the landscape of a C2 attack
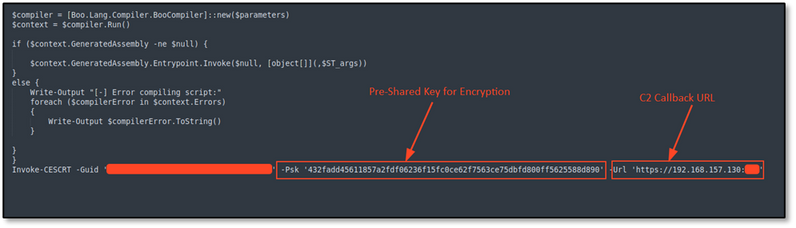
Using NetWitness to Detect Command and Control: SILENTTRINITY C2 - NetWitness Community - 701981
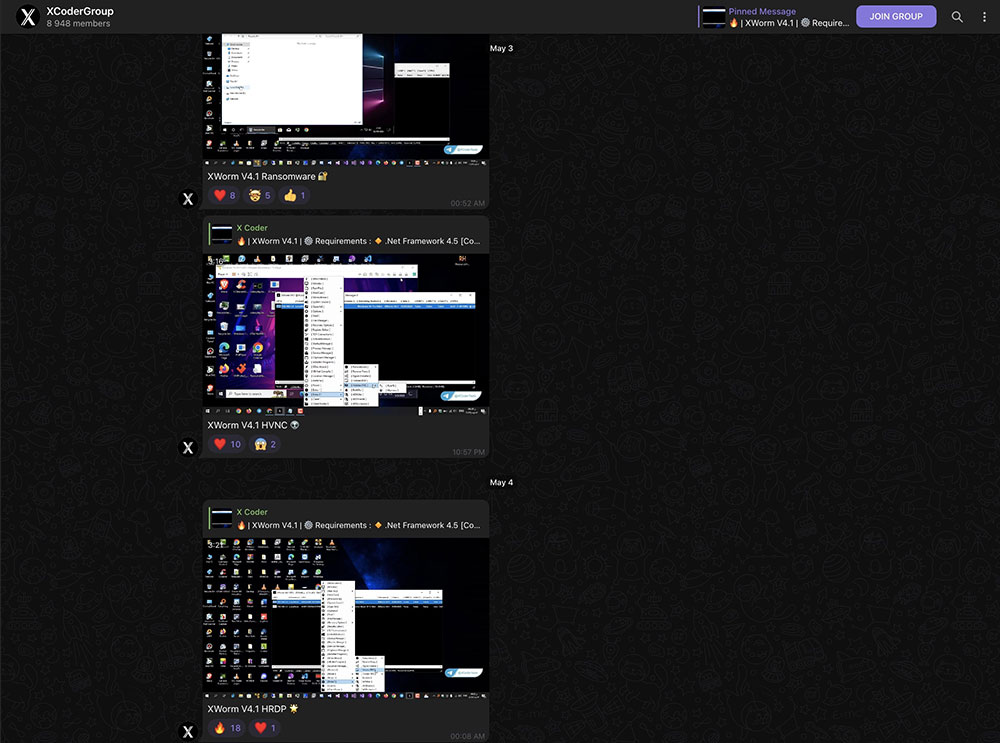
Old Loader, New Threat: Exploring XWorm RAT's Distribution and Tactics