Message Digest in Information security - GeeksforGeeks
A Computer Science portal for geeks. It contains well written, well thought and well explained computer science and programming articles, quizzes and practice/competitive programming/company interview Questions.
A computer science portal for geeks. It contains well written, well thought and well explained computer science and programming articles, quizzes and practice/competitive programming/company interview Questions.
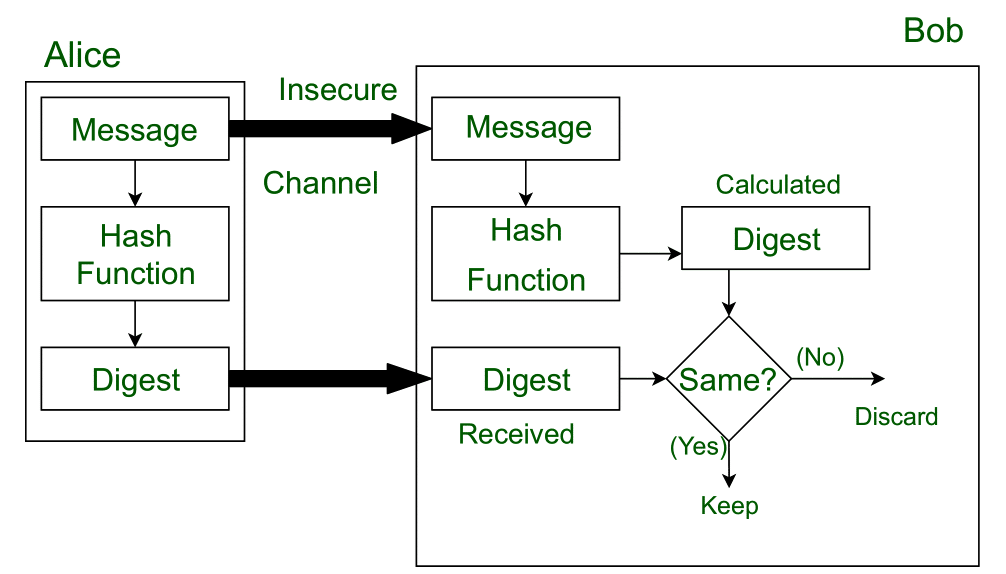
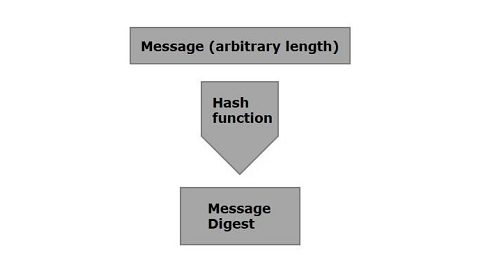
Message Digest is used to ensure the integrity of a message transmitted over an insecure channel where the content of the message can be changed . The message is passed through a Cryptographic hash function. This function creates a compressed image of the message called Digest. Lets assume Alice sent a
What is MD5 (Message Digest algorithm 5)? - UseMyNotes

CSS Question Papers - Explain the relationship between Security
Java Cryptography - Message Digest

58 Combining Security Associations - Case 1,2,3,4, CNS

About Hashing And Its Applications - ITperfection - Network Security

What Is a Message Digest?
What is hashing technique in data structures? - Quora

Key Differences Between CMAC and HMAC - Cbgist
What Is a Message Digest?

PDF) Cryptography Algorithm Gaurav Chhikara

message digest generation in cryptography –

Advanced security model for multimedia data sharing in Internet of

Basics of Cryptographic Primitives for Blockchain Development
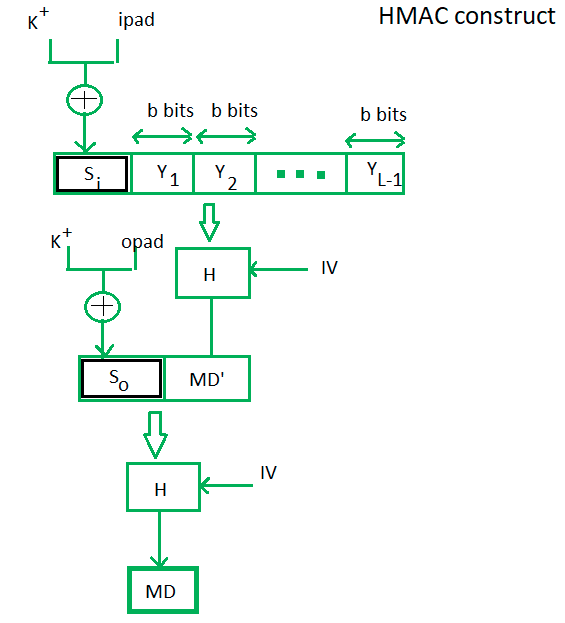
HMAC Algorithm in Computer Network - GeeksforGeeks
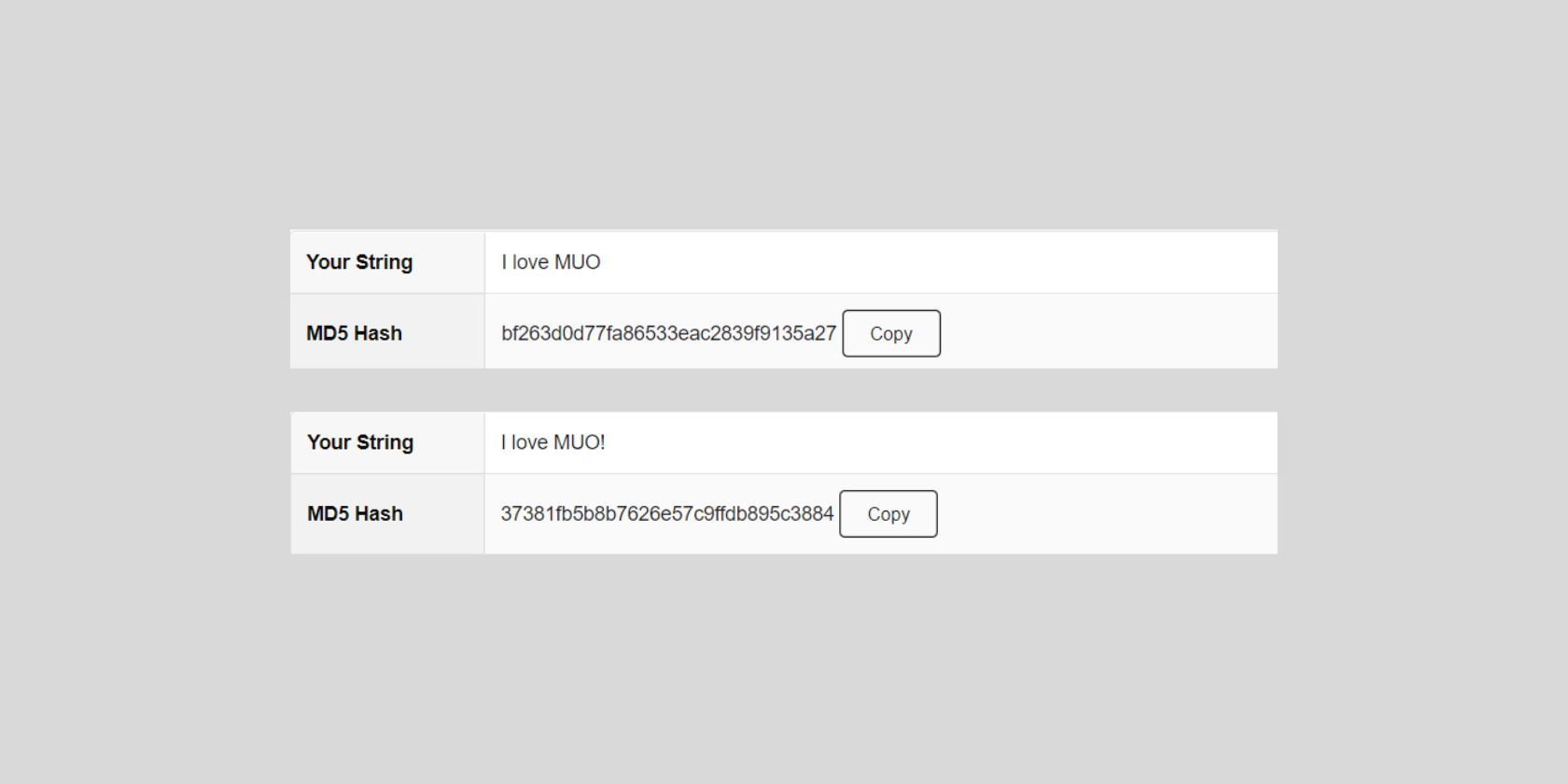
MD5 Hash Algorithm in Cryptography: Here's Everything You Should Know